Part 2: TRASH WORLD NEWS - Tutorial 1
Part 2 - TRASH WORLD NEWS - Tutorial 1So, my old friend Ghast came by and gave me this hacking magazine. Let's have a look.
The cover:

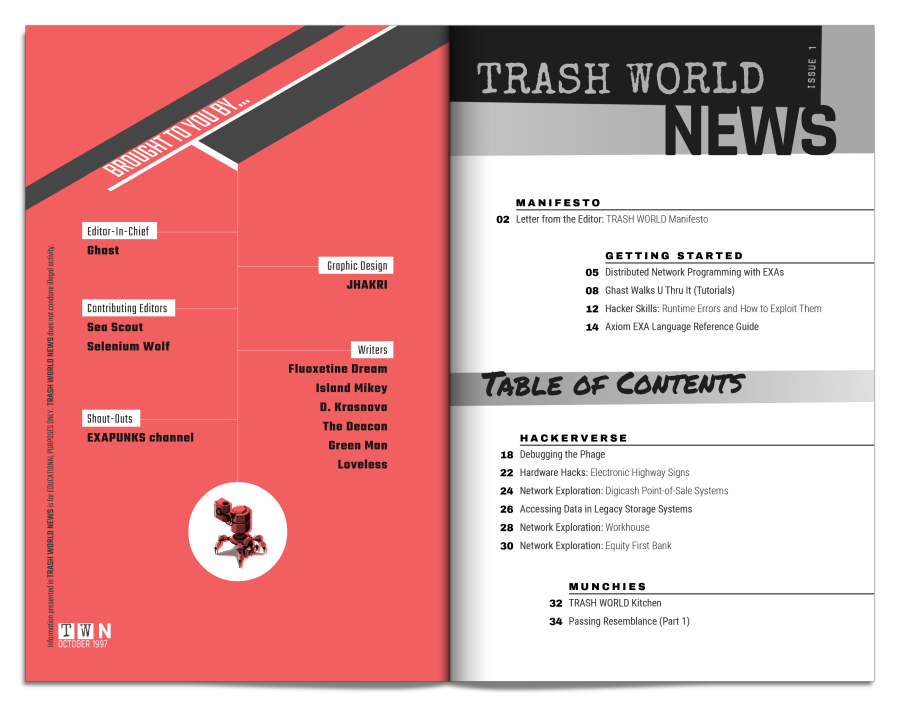
Point of sale systems? Banks? Damn, these people seem to have a lot of insider info. Well, at least there's a "for EDUCATIONAL PURPOSES ONLY" disclaimer to the side. I'm sure that'll help.
Ghast is right you know. Programs and websites run by big corporates... nothing good comes from that. As for the EXAs, I've heard of those but I'm not sure what they do.
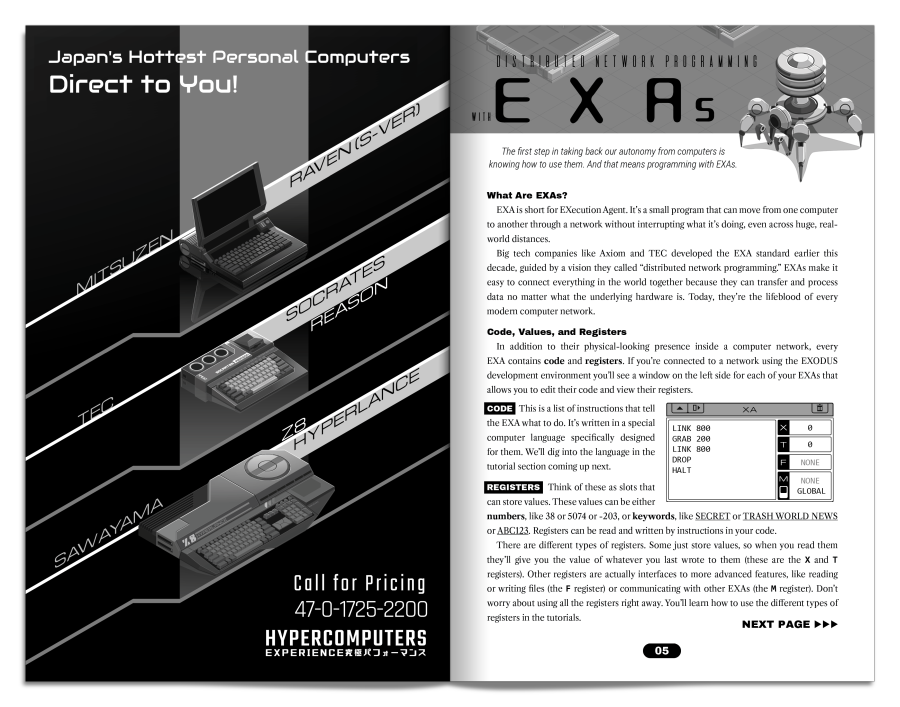
Okay... so to summarize, EXAs are these small programs that move from one computer to another. You can actually see them move around in a network, and they contain code and registers. The code of course tells them what to do. The registers are slots to store values. You can put numbers in, both positive and negative, as well as words, and you can access them from code.
Yeah. That sounds kinda familiar... every EXA acts like a tiny little CPU of its own.
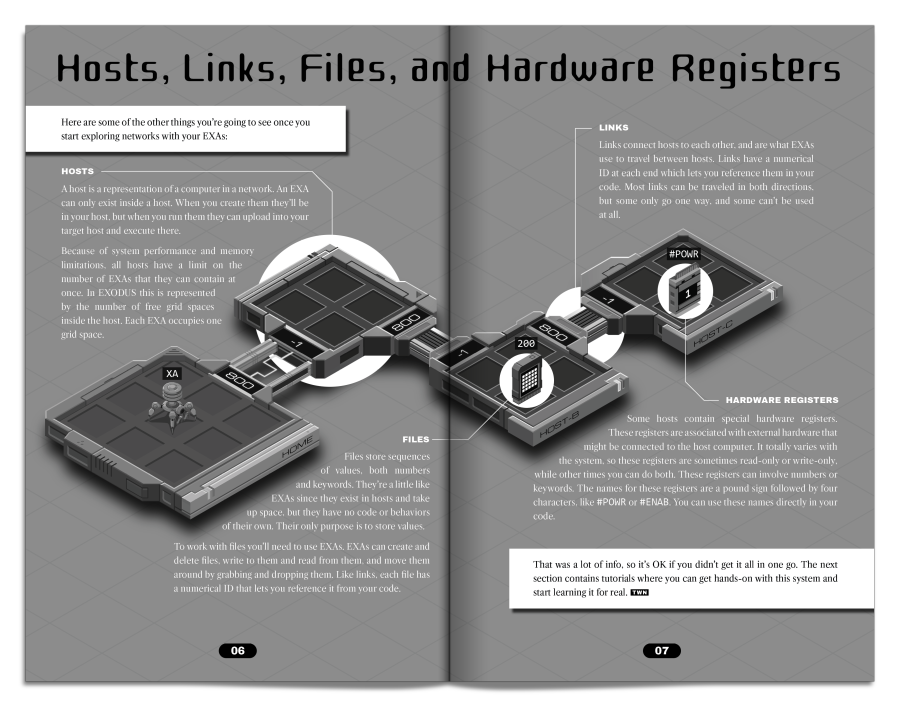
This page explains modern networking. A single computer is called a "host" and it looks like a little platform on the EXODUS programming tool. The number of squares in a host shows how many EXAs can be in a computer at once. Hosts are connected to each other through "links" which can be traversed by EXAs.
There are "files" which can store a lot of values but don't have code. EXAs can interact with files by grabbing and dropping them.
Finally, there's "hardware registers" which are a way for EXAs to talk to the hardware of the host system directly. Not sure what that's useful for but maybe I'll find out.

Hey... something appeared on my computer. I'll leave the magazine on my table so I can look at it at any time.
Looks like =plastered has been busy. Good for them!
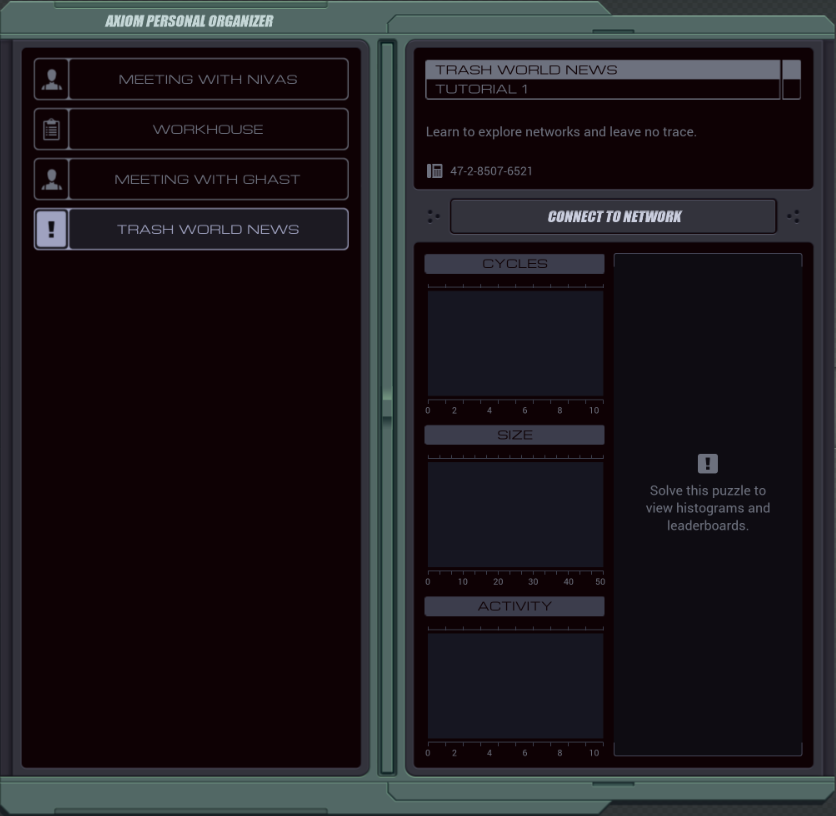
Anyway, a new item appeared in my organizer. Is this what the mysterious lady on my screen was talking about?
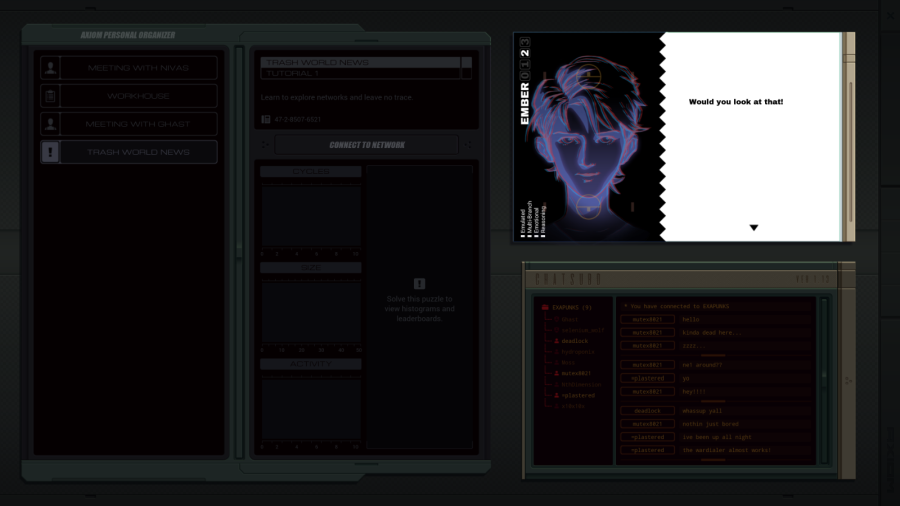
 Actual levels usually start and end with a conversation. These are not voice-acted.
Actual levels usually start and end with a conversation. These are not voice-acted. Would you look at that!
Would you look at that! That zine's got a hacking tutorial in it.
That zine's got a hacking tutorial in it. How about that?
How about that? Funny coincidence, huh?
Funny coincidence, huh? Isn't it?
Isn't it?
I don't really trust her. Why would I interact with her more than necessary?
I guess.
 Oh, come on.
Oh, come on. I timed that just right, didn't I?
I timed that just right, didn't I? Let's continue.
Let's continue.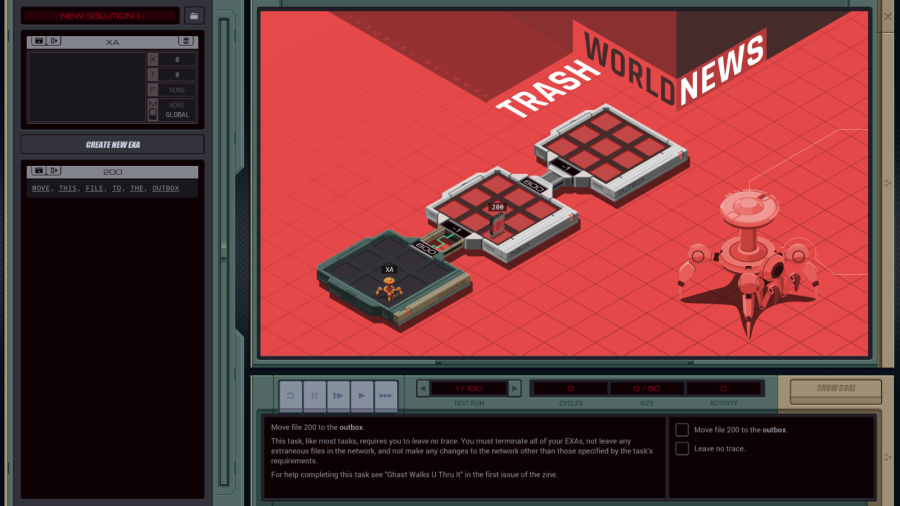
OST: Getting Started
This must be that EXODUS environment mentioned in the Zine. Let's click around a bit and see how it works.
The X at the top right lets me go back to the desktop and organizer. Always good to know.

At the top left, where it says NEW SOLUTION 1 I can put in a name and click the little file icon to save and load multiple solutions. It even has stats for how fast each solution is, so I can optimize my programs. Nice!

I start with one EXA simply called XA which has no code yet, but I can just type it in. I can create more EXAs and name them, but they are limited to two-character names.
Below that I seem to have a file browser, even listing files outside my own computer. I don't know why that works but okay.
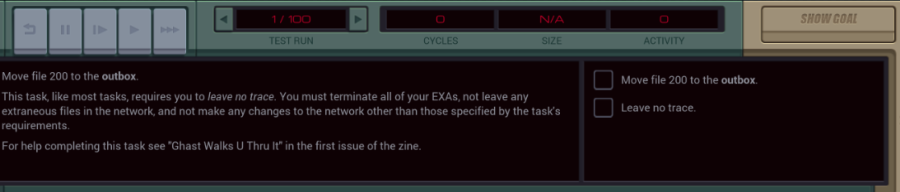
The big screen to the right is obviously my network overview, and the bottom part contains some controls and my goal for this assignment.
Pressing the SHOW GOAL button changes the network overview so that the file is moved to the OUTBOX host and there are no EXAs in sight.
Well, I guess I should check out that tutorial.
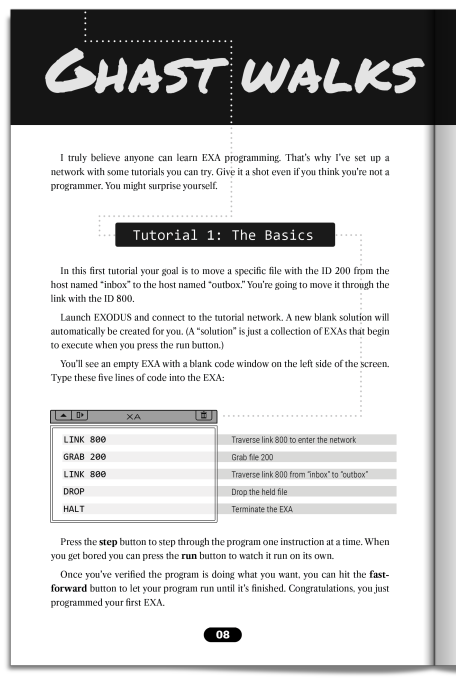
 Since I don't want to overwhelm you folks I'll only post the left page for now, since it's all we need for this puzzle.
Since I don't want to overwhelm you folks I'll only post the left page for now, since it's all we need for this puzzle.Well, this seems easy enough. Just literally copy what it says in the book? I'll give that a try.
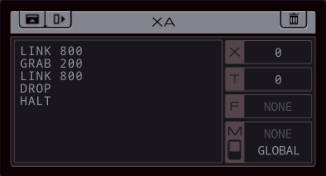
Looks good to me.
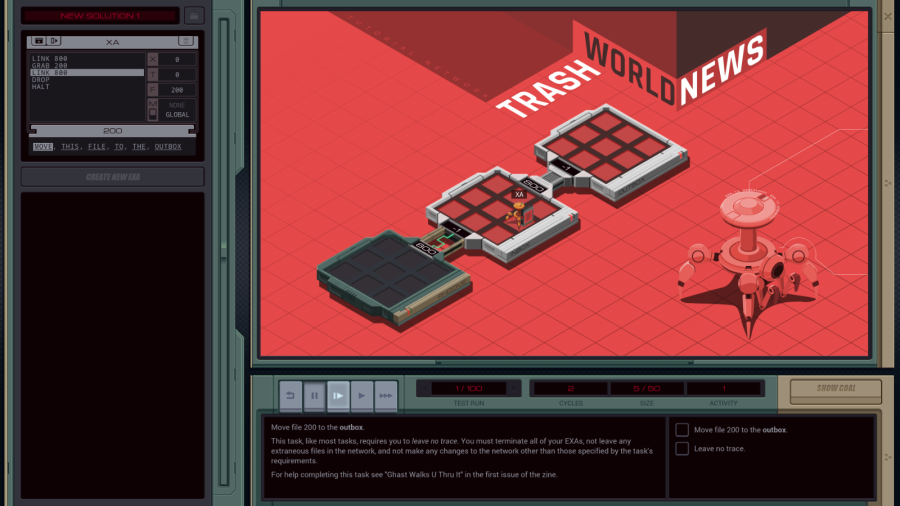
So, the controls at the bottom. From left to right: reset simulation, pause simulation, step through a single cycle (useful for debugging), run (at a watchable speed), fast forward.
Each cycle, every EXA can execute one line of code.
Here I let the simulation run for two cycles. In the first cycle, XA executed LINK 800. That means: from the starting point (my own host, called RHIZOME), traverse the link with ID 800. The EXA ended up in the INBOX host. Then, GRAB 200 caused the EXA to grab the file with ID 200. This was now possible because the EXA and the file were in the same host.

Another LINK 800 operation makes the EXA traverse another link. Since from the point of view of the INBOX, link ID 800 goes to the OUTBOX, that's where the EXA went.

The DROP command lets the EXA drop the file, and finally the HALT command destroys the EXA entirely. The "Leave no trace" goal means you need to either HALT all your EXAs or get them all to come back home.

Once my program is working, the simulation will then run 100 tests at fast forward speed. I guess it wants to make sure my solution wasn't a fluke and actually works all the time.
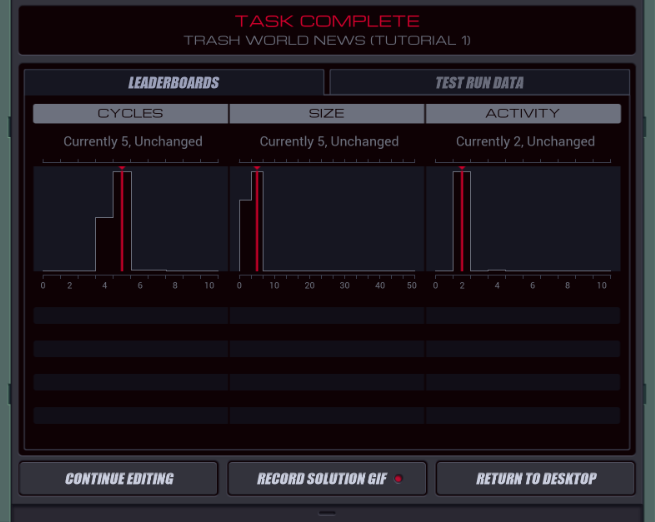
And we get stats. Cycles is the total amount of cycles the program needed to complete. Size is a measure of the amount of lines of code. For both, lower is better. We'll get into Activity later.
 Wait a second, does that say "Record Solution Gif"? That is very kind, game. Don't mind if I do.
Wait a second, does that say "Record Solution Gif"? That is very kind, game. Don't mind if I do.
Neat.
 Now, if you noticed, we didn't have the best score on the leaderboard histogram. Any idea what could improve it?
Now, if you noticed, we didn't have the best score on the leaderboard histogram. Any idea what could improve it?.
.
.
.
.
.
.
.
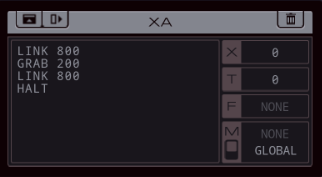
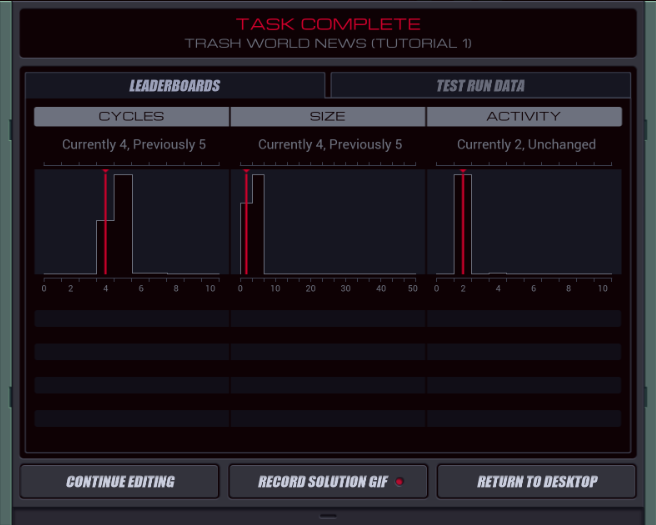
 Turns out the DROP operation is not necessary. An EXA will automatically drop whatever it's holding if it gets destroyed.
Turns out the DROP operation is not necessary. An EXA will automatically drop whatever it's holding if it gets destroyed. It's easy enough to optimize this tutorial level if you know what you're doing. It will get much harder later. I'll probably come up with a reasonable solution or two and leave finding the optimal solutions to the thread.
It's easy enough to optimize this tutorial level if you know what you're doing. It will get much harder later. I'll probably come up with a reasonable solution or two and leave finding the optimal solutions to the thread.
Back in the organizer, we can see our stats, and a new mission appeared.
Also some more talking in the chat.
Finally, the lady behind our assignments has more to say after each assignment.
 I can see everything, you know.
I can see everything, you know. Everything on your computer.
Everything on your computer.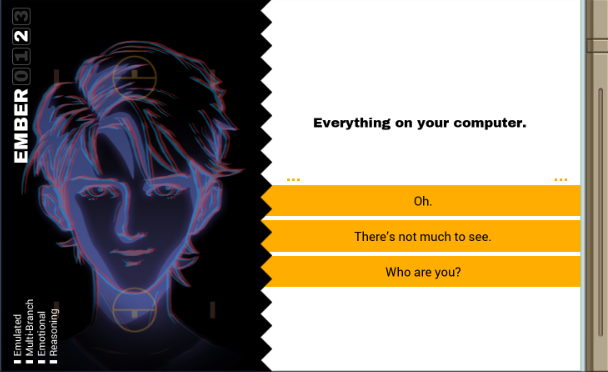
 Even though they're not the most exciting options, for some additional thread participation, I'll see if I can end posts on one of these dialogue option screens.
Even though they're not the most exciting options, for some additional thread participation, I'll see if I can end posts on one of these dialogue option screens.Please vote what our protagonist answers.