Part 1
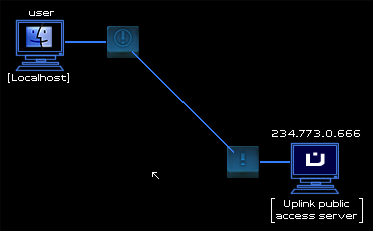
234.773.0.666....
The last decade of my life had been so utterly bleak, so dreary, that looking back it was difficult to remember where one year ended and the other began. The world went on without me, and I continued my miserable existence, wriggling like a tick on a pin: trapped. Frightened. In pain.
Yesterday, I was approached by a complete stranger. A man with a tie, who promised me an end to my pain (could I even remember the cause?). I did not respond, nor did he seem to expect any response from me. Despite my cold, unwelcoming stare, he was actually smiling, and beheld me like he recognized me!
As strange as it was, I could not help but feel that this man understood me, and even knew me. Had he been studying me for some time before making contact?
When I still did not speak, he broke the silence. "I'm sorry it took so long." He handed me a folded piece of paper, and despite my puzzlement and suspicion of the man I immediately snatched it from his fingers. He didn't even flinch, but was positively beaming, like he had just awarded me a diploma or something. "Go now, be free."
He turned around and smartly walked away, leaving me to puzzle over the events that had just transpired. I unfolded the leaf of paper, on which was only written a string of numbers.
234.773.0.666
It didn't take long for me to figure out its meaning:
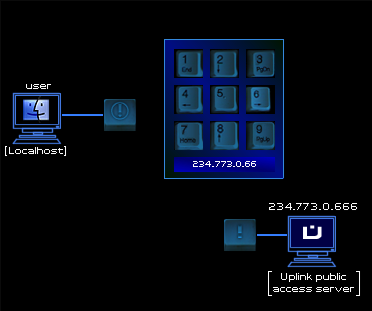
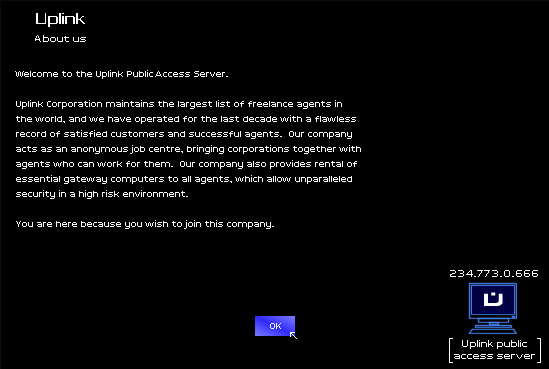
Uplink. This was the way forward I had been hoping for. Reality follows a gaussian curve, and our existences are limited by its laws, but on the internet the only laws that matter, you can eventually overcome.

"About Us" only took me back to the previous screen. It was time to start my career as a cyber-ciminal.
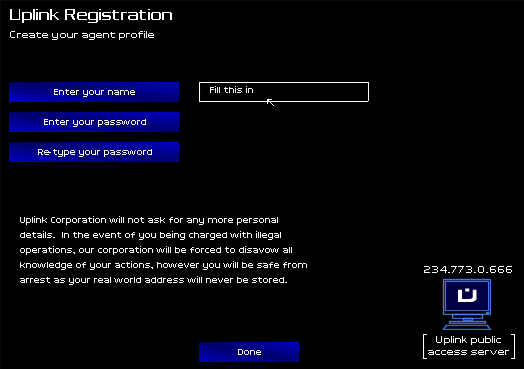
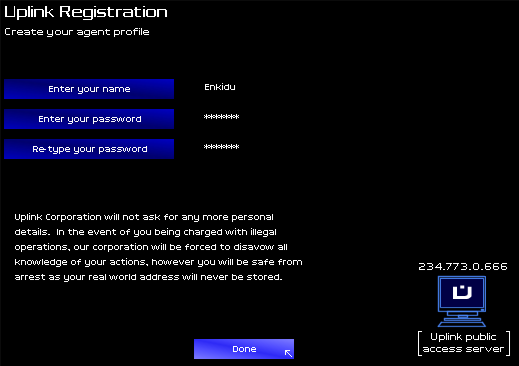
My name... what was in a name? Why do we constrain ourselves to one identity? Multiple personalities make for infinite possibilities, but what name should my actions be tied to for all of history?
There was only one name I could ever use.
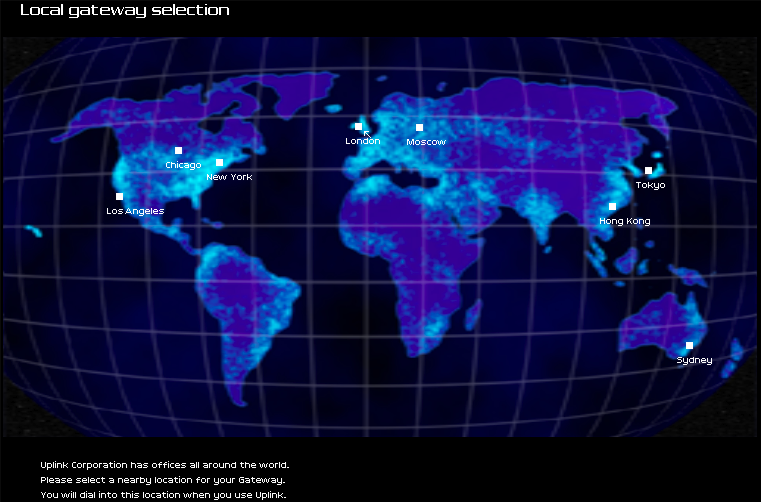
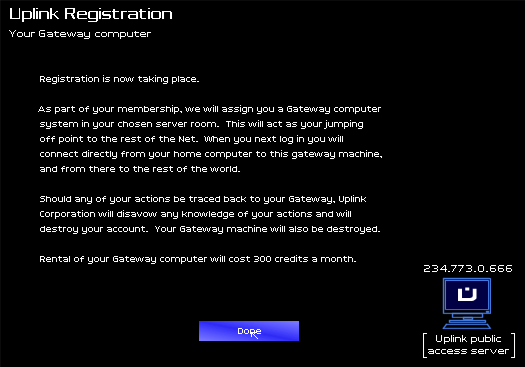
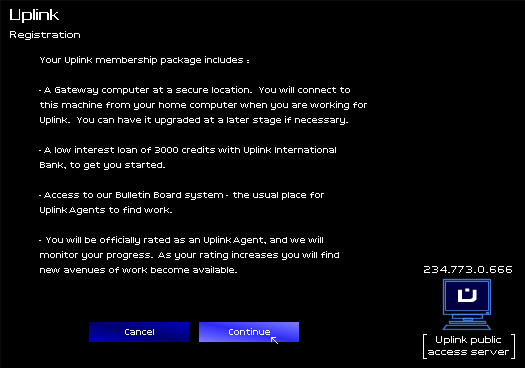
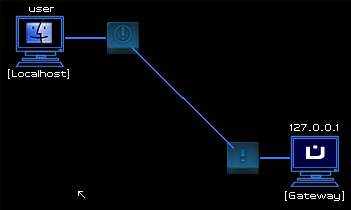
The connection was transferred to my first gateway, a modest and simple machine from where I would launch my first trespasses. Reflexively, I began to interface with it.
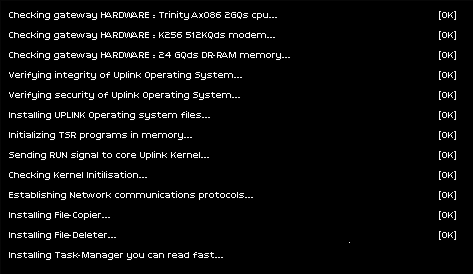
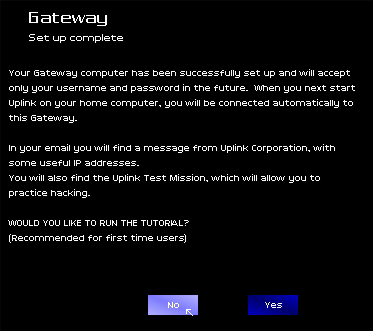
I had never done anything like this before, but declined the machine's offer of a tutorial. If the man in the tie wanted to deal with amateurs, he would have approached somebody else.

Upon declining, I was immediately dumped into the gateway's interface. This would be my home, the goggles through which I would see the world.
At the very top of the screen sat basic information about my computer. Below that sat a number of web links that had come pre-installed with the operating system. On the top right, the world that was at my disposal. This map would show the physical locations of my system, any system I was connected to, and all the systems I was routed through. I noticed that, in the bottom right of the screen, I had already received two emails from The Uplink Corporation, including my first mission:
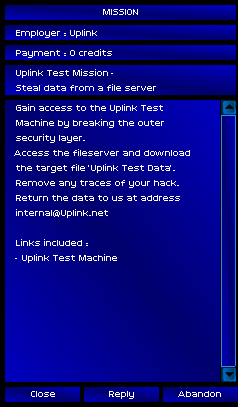
This was an entrance test. I was being watched.
With some trepidation, I connected to the Uplink Test Machine, only to realize I had just made my first mistake:
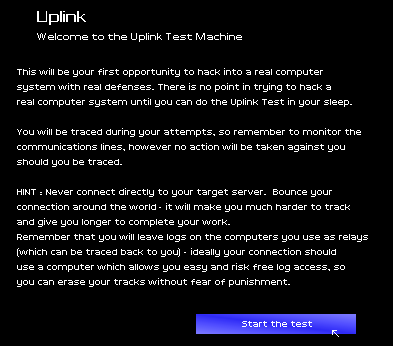
Not only had I directly connected to the computer I was supposed to hack, which had no doubt logged my IP address, but of course the machine was also password protected. Terminating the connection, I pondered how to get past my first obstacle.
I would need tools, and those tools were kept on the Uplink Internal Services System.
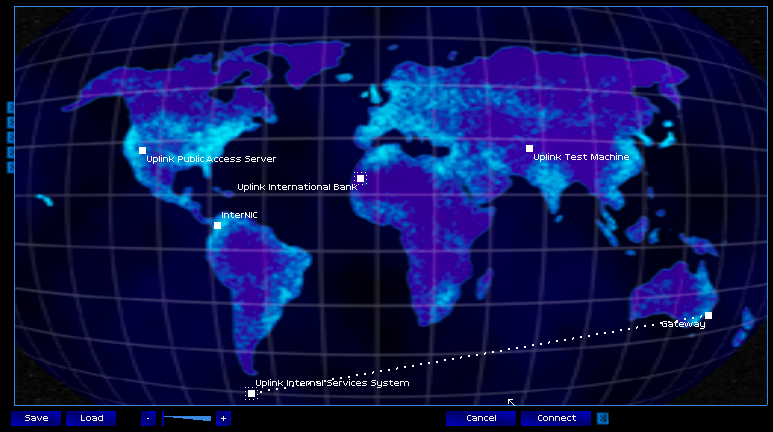
On a remote, abandoned oil rig in the treacherous seas between Antarctica and Cape Horn, a green light winked on, on the secret server as the connection was made. What better place than one of the most deadly areas on Earth, could you hide a server containing some of the most dangerous software on the internet?
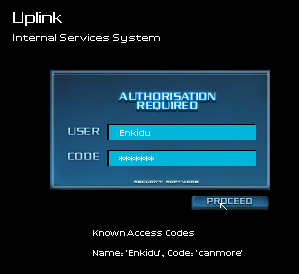
I was greeted once more by a log-in screen, but this one I knew the password to. I was Enkidu, registered Uplink agent and cybernetic mercenary, extraordinaire!
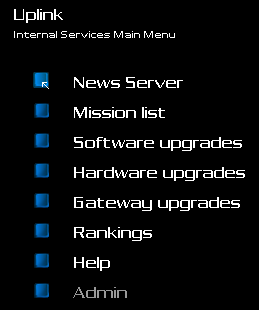
From the main menu I was offered a plethora of services. I decided to explore the server a little bit, so see what I could find to aid me on my mission, starting with news from the hacker scene:
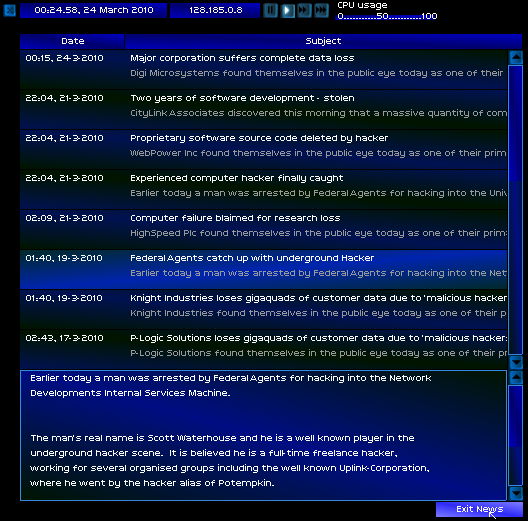
It seemed the life of a hacker was a risky one. In recent years, authorities had begun to crack down with increasing harshness on digital criminals. Though I had never heard of Potempkin until now, I couldn't help but wonder what last mistake, what undestroyed shred of digital evidence had brought his career in Uplink to an end.
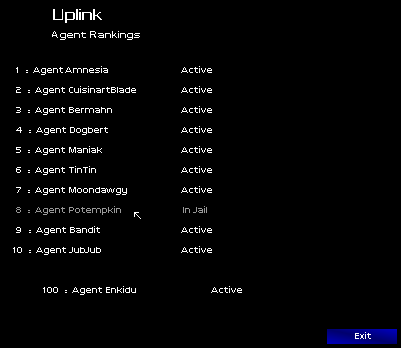
A quick look at the agent rankings told me there was a lot of work to be done if I was to make a name for myself in the underground.
Focus, Enkidu. There will be time for useless trivia later.
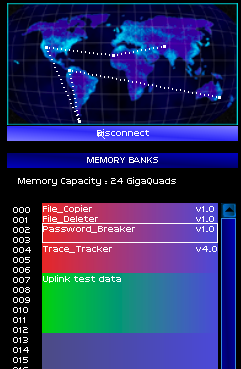
I found what I was looking for in the software upgrades marketplace.
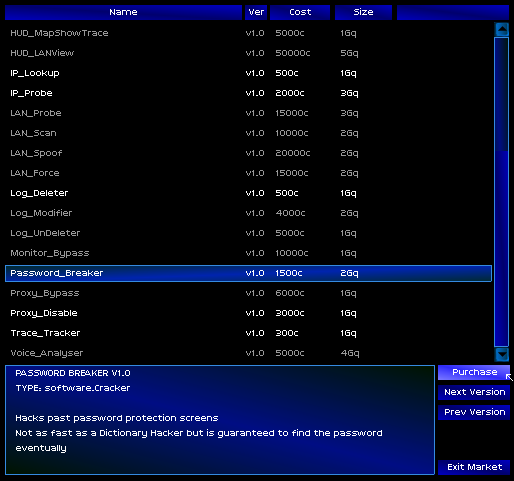
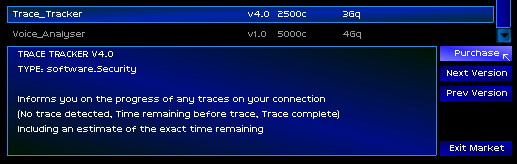
I purchased a rudimentary password breaker, as well as a program that told me whether my connection was being actively traced from the other end. A successful trace by the authorities could be career-ending, and at worst case, this tool would tell me if I was about to be found and warn me in time for me to kill the connection.
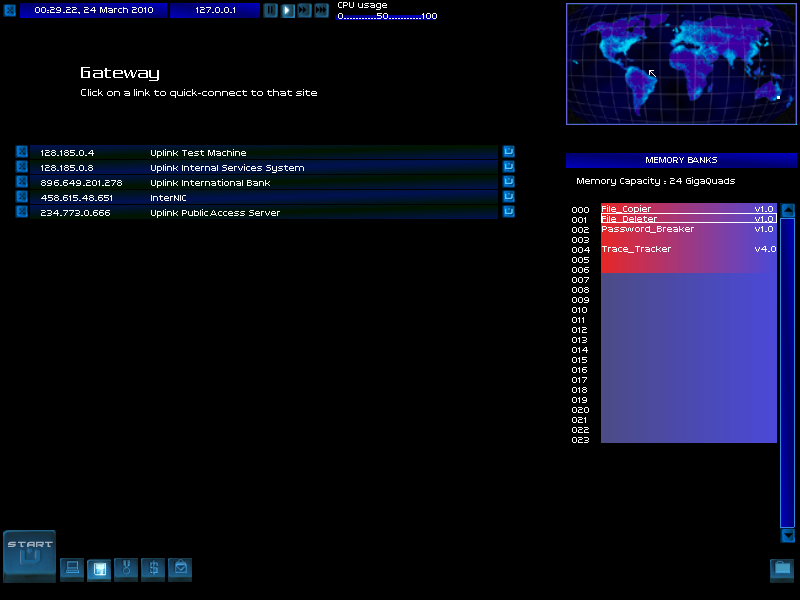
A quick of my memory banks confirmed that I now had the right tools to beat the test.
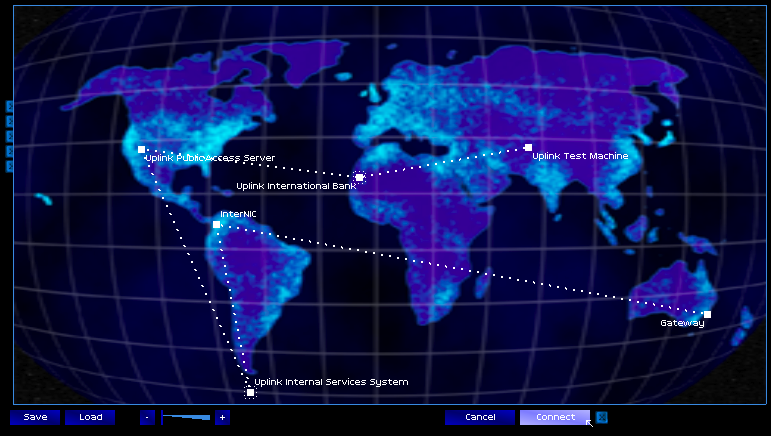
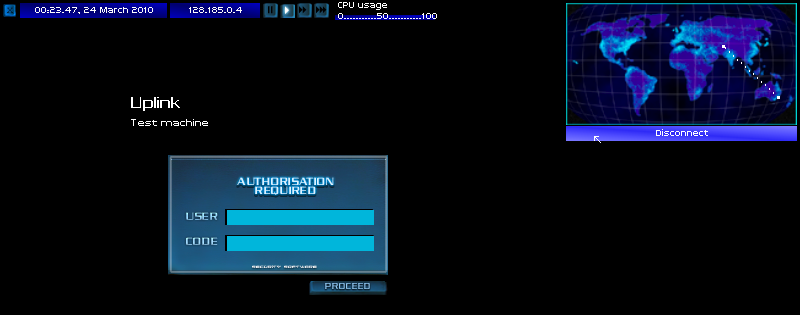
From a connection in Australia, I bounced my signal through four other servers before connecting to the test server. The more complicated my connection, and the more proxies I passed it through, the longer it took to trace from the other end. So long as I was quick enough, I could complete my hack and close the connection before my target ever figured out where it came from.
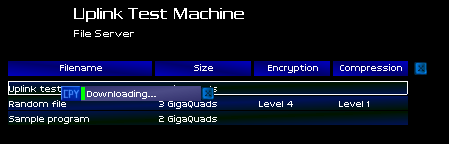
With the trace tracker and password breaking programs both running, I began in earnest.

A glance at the trace tracker at the bottom right of my screen told me I had a little over two minutes before the trace reached me, pinpointing my position. This would be easy. As the password cracker ran, letters and numbers flew over its output screen. One by one, the correct characters locked into place.
Rosebud. I was in! I quickly located my target data, downloaded it, and killed the connection, ending the active trace.

The test data was gibberish. It was nothing but a block of information serving to act as a goal for the test, but I still felt exhilarated. I had pulled it off! Now all I needed to do was send it back to Uplink as proof I had completed the test, and my initiation would be complete!
Earnestly, I composed my email, making sure to attach the file. Signing it, I moved to send it but paused. This would be on record. Men in the future would look back to this email as the one that started my career, to whatever ends of notoriety or fame I was destined. I had to chose my words carefully:
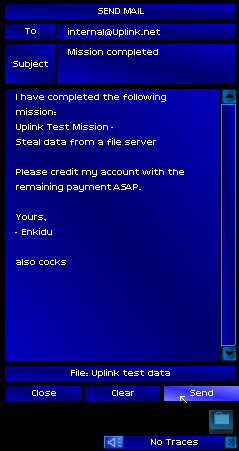
Almost immediately, the response arrived: